ORIGINAL ARTICLE
REIS, Fabiana Candido dos [1]
REIS, Fabiana Candido dos. Software for Risk Management and Patient Safety with Identification Bracelet Printing. Revista Científica Multidisciplinar Núcleo do Conhecimento. 04 year, Ed. 08, Vol. 01, pp. 140-169. August 2019. ISSN: 2448-0959, Access link in: https://www.nucleodoconhecimento.com.br/health/identification-bracelet
SUMMARY
Patient safety is the focus of discussions around the world over the past decade, and is part of the basic criteria for ensuring the quality of patient care, so the adoption of strategies for reducing failures and harmful events in health institutions is Fundamental. Considering computerized risk management an instrument of support for the decision-making of nurses, for recording the identified risks and assistance in identifying others, in addition to presenting a database rich in information for Research. This study aimed to develop a software for risk management and single bracelet printing identification with risk alert signaling for care safety and prevention of adverse events during the patient’s stay in the patient. health service. This is an applied research and technological production The development of this study obeys some phases of a software lifecycle. For the construction of this software, the Scrum methodology was used in the planning phase, in the programming phase, the HTML language (HyperText Markup Language), XML (eXtensible Markup Language) and PHP (Personal Home Page Tools) were chosen because its syntax is quite simple. The softaware of computerized risk management for patient safety focuses on inserting records data regarding the patient and printing the unique identification bracelet with the corresponding stripe color for signaling alerts and attention of Risks. The system consists of 36 access screens and is structured in four modules, they are: the ready-to-care risk classification module is composed of the ACCR Reception protocol; the risk alert module contains 17 risk and attention alerts and evaluation scales; The information module consists of a list of risk factors in each checklist alert for selection and records with blanks for data description and individualization of assistance; the module view bracelet presents the illustration of the bracelet with the data previously recorded by the nurse. We sought with the development of the software the elaboration of the unique identification bracelet with the classification and / or alerts of risks and special care and information visible in the form of tarjada color code, through risk management.
Keywords: nursing, risk management, nursing informatics, patient safety, patient identification systems.
INTRODUCTION
Patient safety has been a discussion agenda around the world since the last decade, and is one of the basic processes to assert the quality of patient care, so the adoption of strategies to reduce errors and adverse events in health institutions is (SANTOS, 2014). Patient protection in health institutions are emerging responsibilities and has been the focus of worldwide discussions (PEREIRA; SOUZA; FERRAZ, 2014).
Brazil (2014) points out that the impulse for patient safety was born at the end of the 20th century, shortly after the publication of the report of the Institute of Medicine (IOM) of the United States of America (USA), entitled as “Err is human: building a more health system (To err is Human: building a safer health system) in 1999, which presented the results of several studies finding that between 44,000 and 98,000 patients died each year in hospitals in that country due to the damage caused by health care.
This publication can be considered as a milestone of confluence on this theme, because from it emerged the era of safety mobilizing many events and studies on patient safety (BRASIL, 2014).
In plotting the trajectory about the history and transformations of patient safety, Nascimento and Draganov (2015) found that since ancient times, although incipient, there was already a responsibility about the theme. They found that the initial milestone took place – with Florence Nightingale in 1852, an English nurse who went to work in the Crimean War (1853 to 1856) and observing the precarious conditions in which the soldiers were, prioritized the safety of soldiers as a factor fundamental to a good quality in the care provided.
In October 2004, the World Health Organization (WHO) formally launched the World Health Assembly, the World Alliance for Patient Safety, formally launched the World Health Assembly. In order to minimize the adverse consequences of unsafe health care and to favor standards and practices of patient safety policies, formulated the Global Challenges for Patient Safety for an international action (WHO, 2005).
The recommendation of the correct identity of the patient was employed by who as the initial international goal of patient safety worldwide and came to be considered the basis of safe care. It consists in the use of identifications, such as bracelets, in hospitalized patients, under observation in the units of emergency care, adults and children, under any condition of care. These are essential procedures for the prevention of damage during health care (REBRAENSP, 2013).
Every multidisciplinary team, including nursing, is responsible for confirming and verifying the identification of the patient during the period that he remains under the care of the institution (BRASIL, 2013).
To develop their work, nursing uses information as a basis, therefore it is necessary to understand what information technology can modify their daily work and to create new opportunities, in addition to directing nursing in order to occupy your space in the face of change processes (SPERANDIO, 2002).
Santos (2010) found that computer science has become relevant to the work process, both care and managerial for nursing, because it allows quick registration and access to patient information, as well as minimizes errors and facilitates communication between professionals.
Edwards (2009) emphasized that in order for access to information to be possible, it is stored and organized into the software, in a file called the database. Pressman (2011) confirmed that the database contains a collection of properly organized information to which you have access through the software.
Based on this principle, the following research question was proposed: “Is it possible to build risk management software with printing of a single patient identification bracelet capable of signaling risk alerts?
Therefore, our proposal is a specific computational program for risk management from an already developed prototype that can benefit the multidisciplinary team in favor of patient safety and, a single means of identification, this being the bracelet, can in a practical, safe and comfortable way contribute to the identification of the patient, as well as with the signaling of risks and peculiar situations that inspire special attention to which it is exposed in the care in health services.
GOAL
Develop software for patient safety management with the printing of a single hazard alert identification and signaling bracelet from prototype software.
MATERIAL AND METHOD
TYPE OF STUDY
This is an applied research and technological production for the preparation of a software for care risk management with proposal of printing of a single bracelet for patient identification and risk signaling for care safety nursing in relation to the precaution of adverse occurrences during the patient’s stay in the health service.
As applied research and technological production, it is understood the generation of new knowledge and processes, for the solution of specific problems with practical objective and operationalization of ideas. Technological research starts from a pre-existing knowledge and, through research and/or practical experience, aims at the materialization of a product, prototype, pilot process or installation (GIL, 2010; MAGELLAn, 2005; SOUZA, 2013).
METHODOLOGICAL PROCEDURES
The development of this study follows some phases of a software lifecycle, the first phase being the construction of a prototype and subsequent development through programming.
Software is defined by Pressman (2011) as being a set of documents that aims to show how the operation and use of programs occur.
Sommerville (2008) states that there are two fundamental software models, generic software that is system developed and put up for sale for any user’s acquisition, such as text processors and custom software that is developed for a specific customer goal and customer.
All software has a lifecycle, which can be considered as a sequence of phases and tasks, which will be performed during the development of a system, that is, the software goes through numerous phases from the beginning, with the generation of ideas to its implementation (PRESSMAN, 2011).
To exemplify these phases, we take a model called cascade, which develops in five phases, are these: definition of requirements, systems and software design, implementation and unit testing, integration and system testing and ultimately operation and maintenance, remembering that the next phase only happens if the previous phase was finalized (SOMMERVILLE, 2008).
PROTOTYPING
For the development of a software it is necessary to choose a methodology or model. There is a range of them, but their choice is given from the definition of interactivity with the user and the amount of documentation that should be developed. Among the most used methodologies is: cascade model, RUP (Rational Unified Process), spiral model, evolutionary, incremental iterative model, extreme programming methodology (XP) and prototyping or prototyping model (PRESMAN, 2011; SOMMMERVILLE, 2008).
Sommerville (2008) defines the prototyping of a system as being a fast version or part of a system, which is developed quickly, with the objective of verifying customer needs as well as the feasibility of some project decisions. This version of the system allows users to experiment before delivery and with this you can refine their requirements. Then, a prototype is considered a prototype version of a software system, which will be used to present concepts, experiment with options and identify problems and solutions.
The advantages of the prototyping model is the possibility of obtaining a version of what the system will be and demonstrate its feasibility, with a small initial investment, the experience gained in the development of the prototype will be extremely useful allowing the reduction in costs in the later stages and resulting in a better designed system, while prototyping problems are related to reconstruction, the customer requires some adjustments in the prototype to make it a product, the recurring changes tend to damage its structure. Adding future changes to the software becomes increasingly difficult (PRESSMAN, 2011).
Pressman (2011) proposes the development of a prototype in six phases, are: collection and refinement of requirements, rapid design, prototype construction, prototype evaluation, prototype refinement and design engineering.
In this study, the first three phases of prototype development were used. In the first phase or phase of collection and refinement of requirements, ideas were discussed, the objectives and content of the software were listed.
The risks would be signaled by means of discreetly colored stripes, without exposing the patient, and the use of more than one or even several colored bracelets is not required to identify risk alerts, as can be observed, currently, in the services of health, and which often makes it difficult to relocate them in cases requiring withdrawal to perform procedures such as punctures and catheter insertions; some discomfort patients refuse to wear loose wristbands, and may cause increased risk of incidents during health care.
Another factor that speaks in favor of building a single device is that daily the nurse evaluates the threats to which patients are exposed and may add or remove an identified risk and with this proposal it would not be necessary to introduce another bracelet, but rather a stripe with the color corresponding to the identified risk and in the case of removal of the risk alert, identified earlier, the colored stripe corresponding to it would then be removed.
The proposed structure for this device consists of a white bracelet that has space for insertion of patient information, such as full name, in children add the full name of the mother, date of birth, hospital registration, barcode and/or QR® code and the stripes in the color corresponding to the risk alert. Colors could be inserted according to the need presented or reported by the patient, that is, as necessary, this solution would avoid discomfort through the use of various bracelets, reduce expenses, besides providing a visualization facilitating and optimizing the working procedure of the health team, also collaborating with the reduction of solid waste from health services.
From the idea of the single wristband model of identification and risk signaling came a second idea necessary to realize the model that was the development of software for risk management of patients, both hospitalized and waiting for care in sectors such as outpatient clinic and emergency room with the preparation and printing of the single bracelet, based on risk management.
With regard to the risk classification in emergency room units, two instruments were highlighted, the accr risk-rated reception and manchester risk rating.
For risk management, 17 alerts were selected, 14 of which were risks and three warning alerts. Risk alerts are: risk of falling, risk of allergy, risk of pressure injury, risk of transfusion reaction, risk of bronchoaspiration, risk of escape, risk of transmissibility, risk of accidental extubation, risk of phlebitis, risk for infection, risk for bleeding, risk for pulmonary thromboembolism and deep venous thrombosis, risk for accidental externalization of nasoenteral probe and risk for suicide. Attention alerts are: to be a practitioner of the religious name -Jehovah’s Witness, to have a need to restrict limb manipulation and be in palliative care, these alerts were considered because they are extremely important in the taking of welfare decision.
The quality indicators proposed by the Hospital Management Support Center (NAGEH) were used a subgroup of the Commitment to Hospital Quality (CQH) maintained by the Paulista Association of Medicine (PMA) and the Regional Council of Medicine of the State of São Paulo (CREMESP), are employed as a guide to monitor and evaluate the assistance and activities of a service and are also understood as performance data for specific processes, products and the organization as a whole (NAGEH, 2012).
The NANDA Taxonomy was used, because nursing diagnoses also supported the content related to risks, considering that the nursing diagnosis is the clinical opinion on the conclusion of the individual, family or community to real and/or potential health problems, being a supplier of the basis for the choice of actions to achieve the long-awaited effects for which nurses are responsible (NANDA, 2015; COFEN, 2009). It is the expression of a situation of the individual who, in our judgment, needs nursing intervention.
In the second phase, the rapid project was elaborated. From the selection of the theoretical framework and the establishment of the requirements of how the system should work, the layout of the screens was built in Microsoft Office Power Point for the system sketch.
From this sketch he went to the discussion with a computer professional with training in systems analysis for the presentation of the proposal and construction of the software-prototype.
The third phase also called the construction of the prototype began with the establishment of an overview of the software, with identification of primary functions that it should perform.
For the construction of this prototype, the Programming languages (Hyper Text Markup Language), XML (eXtensible Markup Language), Java Script and Cascading Style Sheet (CSS) were used for the style of the pages.
HTML® is a language used to expose and define the contents of a web page in a structured format, the only one the browser can interpret for content display, and XML is extremely flexible and easily manipulated by software applications , allows adaptations of the structure of a document to any specific situation, these languages were chosen in this study because its syntax is quite simple (QUIERELLE, 2012; SILVA, 2010).
So-called cascade-style sheets, called CSS are used to describe and customize the appearance of the web content layout, serves to edit the content of pages, such as background color, text styles, content distribution, and images. Thus, CSS are html document formatting archetypes, used using HTML codes (QUIERELLE, 2012).
The system is designed to work on microsoft windows platform. Java Script is the programming language that runs in the browser, is used to create interactive websites and applications for advanced users. (SILVA, 2010).
Java Script is the development layer responsible for all image movement the appearance of the menu and sub menu with several other items in the program, is used to control the HTML information and CSS formatting languages. It is an excellent feature for performing user routines. For this reason java script was used in this project (SILVA, 2010).
To record the information during risk management, questions of the “checklist” type were elaborated, as it facilitates systematization, the process of evaluation and identification of risk alerts. To individualize the assistance were also included free description/writing fields.
SOFTWARE PLANNING, DEVELOPMENT AND FUNCTIONALITY
From the model proposed in the prototyping phase, he went to the discussion with a computer professional with training in systems analysis for the presentation of the proposal, programming and software development.
For the construction of the software from prototyping followed the stages of planning, development and functionality.
PLANNING
In the planning stage, a joint analysis was carried out where a scope was elaborated to organize the development of the project. Structured a model of weekly meetings on four dates, being planned as the agenda of each meeting: presentation and explanation of the prototype by the master, presentation of budget proposal and time for software development, approval of the budget by the master and discussion of the agile methodology for software development by the programmer, finally the contract was signed and delivery of schedule for the start of activities in the following week.
It should be noted that the methodology proposed for the construction of the software will be Scrum, agile management for projects in this segment. Scrum is a fast, easy and lightweight framework, used for the management of the expansion of complex products integrated with complex environments. Scrum makes use of an iterative and incremental interappeal to add regularity value, reducing project risks (SABBAGH, 2017).
Rubin (2018) demonstrates that in Scrum, cycles are called Sprints. They carry fixed dimension and succeed one after the other, without interruptions between them, that is, everything in a project that uses Scrum happens within the Sprints. Each Sprint consists of:
- Sprint Planning Meeting, where Sprint planning takes place;
- Product development work, which includes everything that is needed to deliver a portion of sprint’s ready-made product;
- Daily Scrum meeting, integrated in everyday development, which is a daily meeting to generate visibility and plan the next day of development;
- Sprint Review Meeting, in which the results of the development carried out in Sprint are demonstrated to customers and other stakeholders, offering their feedback;
- Sprint Retrospective meeting, where the team judges what went well and what needs improvements in their way of work;
- Any additional scheduled meetings or sessions that are required, the sample view, the Release Planning meeting, and the Product Backlog Refinement sessions.
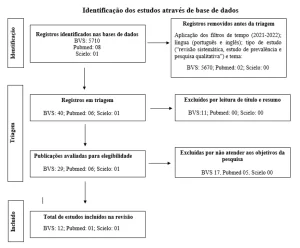
Figure E represents scrum interaction, indicating the succession of elements present in all cycles (or Sprints) and the succession of cycles.
Figure A: Interaction or succession of scrum cycles (Sprints)
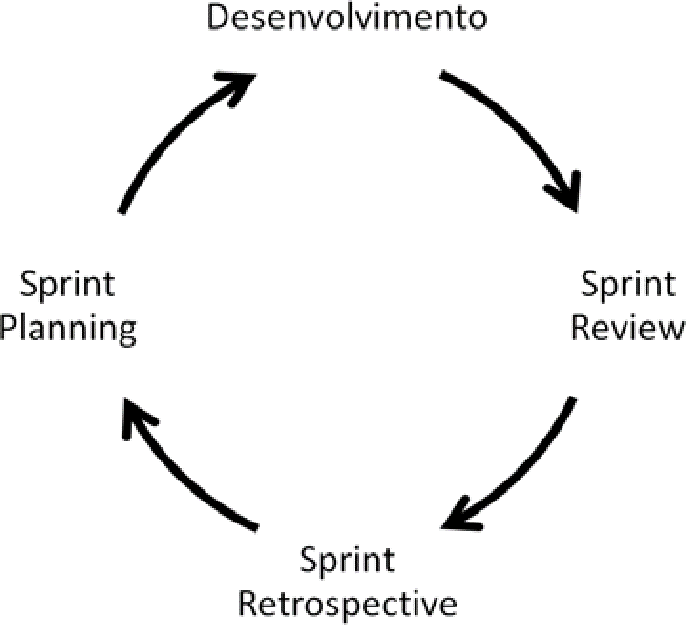
Sprint starts with the Sprint Planning meeting, where the work to be done in sprint itself is planned. At this meeting, the Development and Product Owner Team wake up from the top items of Product Backlog, about what will definitely be developed. That is, simplified by ScrumMaster, you select a set of topics from the top of Product Backlog that propose development capacity during Sprint, a preview, and set a business goal to be achieved with the prosperity of these items, called the Sprint Goal. Thus, the Development Team is committed to achieving the Sprint Goal (KNAPP et.al, 2017).
The Development Team is for a maximum of fifteen minutes on each day of development work, at the same time and place, for the Daily Scrum meeting. The objective of the meeting is to ensure the transparency and visibility of your work with each other and plan, even informally, the next day of production (RUBIN, 2018).
The archived feedback of customers, the master’s master at the Sprint Review meeting in this case, is required by The Product Owner as raw material for changes in Product Backlog – to change the product in the process of generating, seeking to better meet the needs of consumers (SABBAGH, 2017)
Sprint Backlog is a list of items selected from the top of the Product Backlog for the development of Product Increment in Sprint(what), added from a plan of how this work will be performed(how). Product Backlog refinement is the act of adding details, estimates, and orders to items in Product Backlog (KNAPP et.al, 2017).
Figure B: The Scrum Cycle
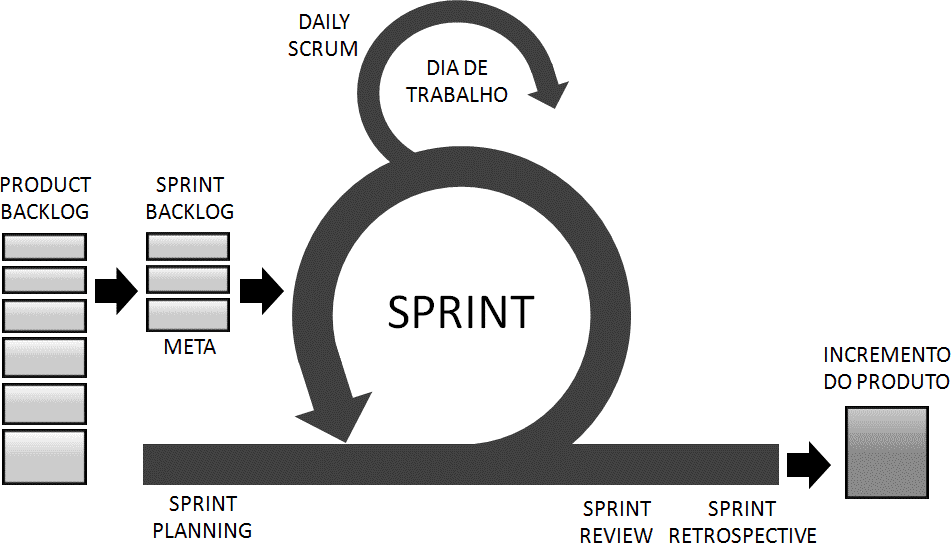
Through regular Releases, scrum team gets feedback from product users and can thus reduce risks and produce the right product. The Scrum Team also enables a sense of progress of the project to its customers and stakeholders, and can have bonuses to the investment made by the project’s clients (RUBIN, 2018).
Rubin (2018) states that there may be a Release Planning meeting for each Release, which is held at any given time before the work begins for the corresponding Release, which should happen during the last Release Sprint.
DEVELOPMENT
PHP® or PHP Hypertext Preprocessor, means that the product was initially titled “Personal Home Page Tools”; and growing with a goal, a new and more appropriate name was elected by community vote. The dimension “.php” is advisable to designate a PHP file® (SKLAR, 2004).
PHP® is a script creation language encrusted in HTML® on the server. PHP can be considered as a collection of HTML supertags® that add server charges to your web pages. You can make use of PHP to immediately build a complex Web page (SOARES, 2013).
PHP® does not get a direct relationship with layout, events, or everything that involves the appearance of a web page. Much of what is accomplished by PHP is invisible to the end user. When you view a PHP page, you won’t be able to say that it wasn’t written in HTML®, because the final result of PHP® is HTML®.
HTML® is a language used to expose and define the contents of a web page in a structured format, the only one the browser can interpret for content display, and XML is extremely flexible and easily manipulated by software applications , allows adaptations of the structure of a document to any specific situation, these languages were chosen in this study because its syntax is quite simple (QUIERELLE, 2012; SILVA, 2010).
SOFTWARE
Software is the modifiable set of instructions, ordered and logical, directed to hardware for the execution of processes required to solve necessary procedures, to troubleshooting and tasks of data processing. Software ratings are divided for the purpose of use, being basic, application/application and programming language (SOMMERVILLE, 2011).
FINAL PRODUCT
The final product consists of a white bracelet that has space for insertion of patient information, as a full name, in children add the full name of the mother, date of birth, hospital registration, barcode and/or QR® code and the tarjas in color corresponding to the risk alert. The colors could be inserted according to the need presented or reported by the patient, that is, as many as necessary.
RESULTS
GERIS – SOFTWARE FOR ASSISTANCE RISK MANAGEMENT WITH UNIQUE BRACELET PRINTING PROPOSAL
The proposed name for the software was GERIS, which comes from the initials of the words Risk Management. The system consists of a computer program with the objective of supporting nurses in decision making during assistance to the individual through the mapping of care risks.
To elaborate the project, there was initially a phase of data collection and requirements definitions developed by the prototype author. The content of the prototype is based on instruments and tools related to nursing care practice, as quality indicators; nursing diagnoses and official documents issued by the Ministry of Health, as well as other literaturefound in specialized databases and books.
Table 01 – Theoretical rationale for the construction of instruments and risk alert
| Information | BRASIL (2013, 2014a, 2013b); FIOCRUZ/Proqualis(2014); Gomes (2008); Hinrichsen (2011); Manual de Indicadores de Enfermagem NAGEH (2012); NANDA (2015); Lima, Melleiro (2011), Oliveira(2014). Siqueira (2015); Zárate-Graiales. et al.(2015); ANVISA (2013); American hospitalassociation (2008); ABNT (2010); Barcelos (2016); Costa, Meirelles, Erdmann(2013); Fassini (2012);Fawkes (2007) Hemesath (2015)Hoffmeister, Moura (2015); Milagres (2015); Neves,Melgaço (2001); Norris, Ranger (2009); OMS (2010); Pimenta et al. (2015); Public health and clinical systems (2014); Santos (2014); Smith et al. (2011); Sperandio (2002, 2008); Silva (2013); WHO(2007b); |
| Risk classification instruments | BRASIL (2009 e 2004); Servin (2010);Amthuer(2015); Diogo (2007); Acosta, Duro, Lima (2012); Souza (2009); Duro (2010) FITZGERALD(2012) |
| Allergy risk | Ribeiro (2015); NANDA (2015); |
| Risk of bronchoaspiration | NANDA (2015); |
| Risk of accidental extubation | NAGEH (2012); Barcellos et al. (2016); Carvalho (2010); Castellões, Silva, (2007, 2009); Duarte(2016); Neto et al. (2014) |
| Risk of escape | Vieira; Dall’agnol (2009); Vieira (2005); COREN(2010b); |
| Risk of pressure injury | NAGEH (2012), NANDA (2015); Laurenti et al.(2015); Lyder, Ayello (2008); Paranhos (1999); Freitas, Alberti (2013); SANTOS et al. (2015); |
| Risk of falling | NAGEH (2012); Severo et al., (2014); NANDA(2015); Urbanato (2013); American geriatrics society (2010); Sociedade brasileira de geriatria egerontologia (2008); |
| Risk of transfusion reaction | BRASIL (2010) |
| Risk of transmissibility | Lacerda (2014); BRASIL (2010); Andrade (2013); |
| Risk for accidental externalization of sondanasoeteral | NAGEH (2012); Pereira (2013); |
| Risk for phlebitis | NAGEH (2012);Milutinović, Simin, Zec (2015); Marinho (2011); Tertuliano (2014); Ray-Barruel etal. (2014); |
| Risk for infection | Almeida (2014); NANDA (2015); |
| Risk for bleeding | NANDA (2010) |
| Risk for deep vein thromboembolism | Caramelli et al., (2004); Okuhara et al. (2015);SBACV (2015); Veiga et al. (2015) |
| Jehovah’s Witness | França (2008); Takaschima (2016); COREN (2013); |
| Limb restriction | BRASIL (2016); |
| Palliative care | CREMESP, 2008; Faller (2016); Guimarães (2016); Lima, Oliveira (2015); Oliveira et al. (2016) Gomes, Othero (2016);Evangelista et al. (2016); BRASIL (2002); Santos, Oliveira, Feijao (2016); WHO(2002); |
| Risk for Suicide | NANDA (2015); MS (2006); BRASIL (2006); OMS(2000); Bertolote, Santos, Bortega (2010);CREMESP (2008); |
Source: Santana, 2017 – Prototype Software Development for Risk Management and Patient Safety with Identification Bracelet Printing.
To compose the patient’s risk management and safety system, called GERIS, 17 alerts were selected, 14 of which were risks and three warning alerts.
Risk alerts were: risk of falling, risk of allergy, risk of pressure injury, risk of transfusion reaction, risk of bronchoaspiration, risk of escape, risk of transmissibility, risk of accidental extubation, risk of phlebitis, risk for infection, risk for bleeding, risk for pulmonary thromboembolism and deep venous thrombosis, risk for accidental externalization of nasoenteral probe and risk for suicide. Attention alerts are: to be a practitioner of the religious name Jehovah’s Witness, to have a need to restrict limb manipulation and be in palliative care, these alerts were considered because they are extremely important in the taking of welfare decision.
In the composition of alerts, care risk scales were also included to support the identification of risks or attention.
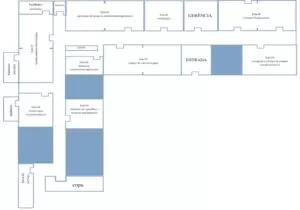
The system contains 36 screens, which will present themselves as follows:
- Professional access and registration screens – 04 screens
- Home menu screen – 01 screen
- Patient search and registration screens – 03 screens
- Screens Module Risk Classification – Emergency Care and Assistance Risks – 02 screens
- Screens Risk Alert Module – 01 screen
- Screens Module Alerts and risk attention information and evaluation scales – 24 screens
- Screens View Bracelet – 01 screen
The information from the “patient menu” icons has been pre-established in advance, so that the user can access it only with one tap on the input device (mouse).
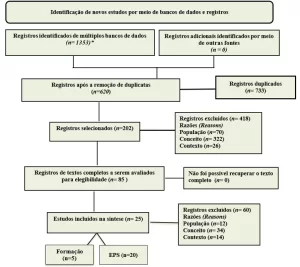
For the development of the software, the logic presented in the diagram below was obeyed:
Figure C: GERIS software diagram
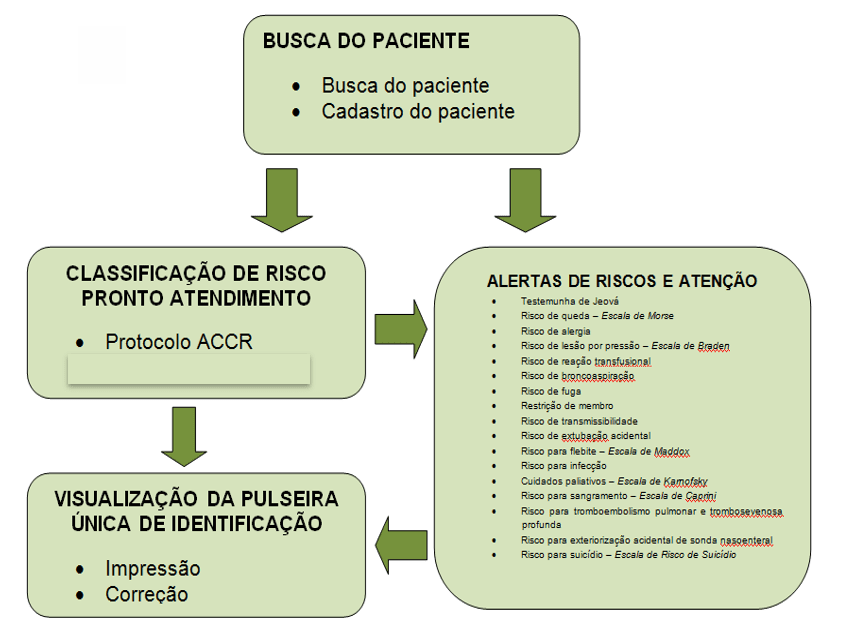
In the Risk Classification Module – Prompt Service the system will be structured in phases referring to the classification and risk management process. The phases called: Risk Classification for Emergency Care contains the Manchester protocol and the reception protocol with risk classification, proposed by the Ministry of Health, with care options according to the signs and symptoms of the individual.
In the Risk Alert Module, the identification and selection of alerts likely to cause incidents during health service assistance will be designed, and the risk-specific information registration icon, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk-specific assessment option, with a risk- risk scales, enabling the preparation of risk alerts that should be managed by nurses, through the use of this database previously established by the system, and automatically generate the identification bracelet with the stripes in the corresponding colors.
In the Information Module will be listed the risk alerts and attention for nurses to select the appropriate alerts and enter the data for it, as defined in the pre-established checklist, will be chosen for selection items to provide the nurse with less time with the role and greater availability direct patient care, these records may be stored and consulted and updated, also provides data for statistical research purposes. Some alerts will complement the risk assessment scale for recording the score.
In the View Bracelet Module after the nurse has made the risk rating or selection of risk alerts or even both for the same patient he can see the illustration of the single bracelet with the colors of the stripes chosen for data conference and print after confirmation or opt for correction on the appropriate icon.
The screens will be developed with light and standardized colors, tasks with different information will be divided into different screens, to facilitate the user’s memorization, and this separation will be made with the use of input icons. The menu displayed contains options for content information.
Figure D: Professional access screen
The professional access screen aims to ensure secure accessibility to the system, considering traceability requirements related to date, time and nominal user access. As mentioned in Figure J, the previous registration will allow the preparation of login and individual password allowing access to the software.
Source: Author.
Figure E: Patient Menu Screen: modules
Source: Author.
Figure F: Ready-To-Face Screen: ACCR Risk Rating
When selecting the “ready-to-care” icon on the patient menu screen: modules (see figure N) you can click the ACCR icon to perform the risk rating for patients admitted to the prompt. On the screen ready attendance: Risk classification ACCR it is necessary to complete the following information on the screen in question: medical record number, public or private agreement and date and time of admission.
At the end of the fill, you must click the blue button “continue” to continue the previously selected risk rating.
Source: Author.
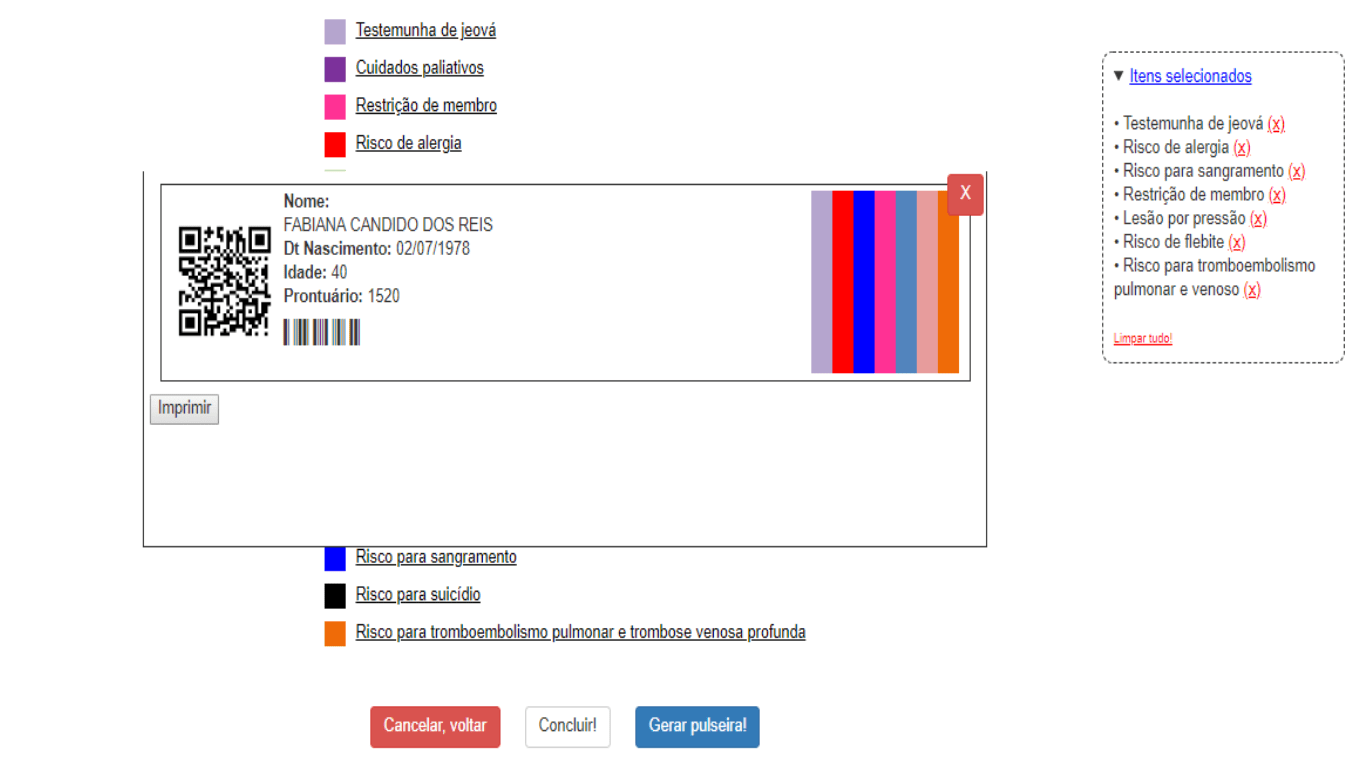
Figure G: Screen Risks Assistance
The care risk screen is present in two icons on the patient menu screen: modules (see Figure N), are they prompt care and hospitalization. It is possible to choose the area in which the patient is being admitted or reclassified. This screen offers the option of fourteen assistance risks and three risk alerts. The Nurse must click the desired option and continue the classification.
On the direct side of the screen you can check the risks and alerts already classified, in “selected items”, and it is possible to keep them or delete everything!” before printing the color identification bracelet. This feature aims to ensure a revision or update of the classification before printing the bracelet.
At the end of the fill, you must click the blue button “generate bracelet” to view the layout of the bracelet to be printed (see Figure AI) or click the white button “cancel, return” to abort the classification performed.
Source: Author.
Figure H: Screen “view bracelet”
The display of the identification bracelet with colored stripes according to the risks and alerts classified presents on the screen of “care risks” (see figure M), the blue button “generate bracelet” was programmed to finalize the classification and result in the printing product.
On the right side of the screen you can check the risks or alerts chosen during the patient’s assessment and check the bracelet before printing. If any risk and/or alert increases or subtraction is required, you can close the bracelet generated on the red button and o n the same screen to continue the correction. To subtract a risk and/or alert at the time of the bracelet it is necessary to go on “selected items” and click on th
n the same screen to continue the correction. To subtract a risk and/or alert at the time of the bracelet it is necessary to go on “selected items” and click on th![]() e symbol or to cancel all, just click “clean everything!”. In case of increased risk and/or alert, only continue the classification of the desired item after the wristband closes.
e symbol or to cancel all, just click “clean everything!”. In case of increased risk and/or alert, only continue the classification of the desired item after the wristband closes.
FINAL CONSIDERATIONS
Patient safety has been the subject of discussions and studies in Brazil and around the world, and has become the focus of all health institutions.
Patient identification is the first international patient safety goal and considered paramount, when followed the protocol correctly, to avoid errors and incidents that cause harm to the patient.
Identification bracelets have become usual in most institutions, mainly hospital, due to ease of implantation and efficacy in identification. They are also choices to alert risks and assist in identifying clinical information.
However, they are often misused, as well as colors that signal a risk or clinical information, are not standardized, facilitating the occurrence of the error.
The technology began to be used on a large scale in patient safety and risk management. Health information and communication technology has become fundamental in the computer age. Electronic medical records, placed in complex systems and software, standardize and effect records, ensuring access to information and minimizing errors in multi-disciplinary communication on a large scale.
In this way, create software that meets the need to standardize and minimize the error in patient identification, where nurses classify risks and prescribecares care for these risks in electronic databases and easy access to everyone, as well as compiling all information and alerts on a single bracelet would be a big step in providing safe care.
REFERENCES
AGÊNCIA NACIONAL DE VIGILÂNCIA SANITÁRIA (ANVISA). Rede sentinela – histórico. Disponível em: http://www.anvisa.gov.br/servicosaude/hsentinela/historico.htm. Acesso em: 28 out. 2018.
AGÊNCIA NACIONAL DE VIGILÂNCIA SANITÁRIA. Assistência segura: uma reflexão aplicada à prática. Segurança do Paciente e Qualidade em Serviços de Saúde. Brasília: ANVISA, 2013.
ASSOCIAÇÃO BRASILEIRA DE NORMAS TÉCNICAS (ABNT). ABNT NBR ISSO 31000. Gestão de riscos – Princípios e diretrizes. Rio de Janeiro: ABNT, 2010.
ASSOCIAÇÃO BRASILEIRA DE NORMAS TÉCNICAS. Tecnologia de informação Processos de ciclo de vida de software. Rio de Janeiro. 1998. Disponível em:
<http://aulasprof.6te.net/Arquivos_Aulas/06Qualidade_Soft/ABNT_NBR_ISO_12207. pdf> Acesso em: 18 jan.2019.
ÁVILA, A, M. Identificação por radiofrequência: tecnologia inteligente, hospital eficiente, qualidade e segurança para o paciente, 2012. Monografia (Especialização em Informação Científica e Tecnológica em Saúde) – Informação Científica e Tecnológica em Saúde, Fundação Oswaldo Cruz, Porto Alegre, 2012.
BAKKEN, S. S. et al. PHP Manual. Disponível em: <http://br.php.net/get/php_ manual_pt_BR.chm/from/this/mirror>. Acesso em: 20 mar. 2019.
BATTISTI, Júlio. Apostila de Hardware. Banco de Tutoriais do site Júlio Battisti, 2009. Disponível em: Acessado em 26 de abril de 2019.
BRASIL. Ministério da Saúde. Agência Nacional de Vigilância Sanitária. Resolução nº 36, de 25 de julho de 2013. Implantação do Núcleo de Segurança do Paciente em Serviços de Saúde. Diário Oficial da União25 jul 2013; Seção 2. Disponível em: <http://bvsms.saude.gov.br/bvs/ /anvisa/2013.htm> Acesso em: 15 ago. 2018.
BRASIL. Ministério da Saúde. Gabinete do Ministro. Portaria MS/GM nº 529, de 1 de abril de 2013. Institui o Programa Nacional de Segurança do Paciente (PNSP). Diário Oficial da União. 2013b. Disponível em: <http://bvsms.saude.gov.br/bvs/saudelegis/gm/2013/prt0529_01_04_2013.html> Acesso em: 15 ago. 2018.
BRASIL. Ministério da Saúde; Fundação Oswaldo Cruz; Agência Nacional de Vigilância Sanitária. Documento de referência para o Programa Nacional de Segurança do Paciente. Brasília – DF, 2014. Disponível em: <http://bvsms.saude.gov.br/bvs/publicacoes/documento_referencia_programa_nacional_seguranca.pdf> Acesso em: 06 ago. 2018.
CANDIDO, A. H. L; JUNIOR, KW. Design de produto e a pratica de construção de modelos e protótipos. Publicado em LDSM – Laboratório de Design e Seleção de Materiais.2009.
CONSELHO FEDERAL DE MEDICINA; SOCIEDADE BRASILEIRA DE INFORMÁTICA EM SAÚDE. Cartilha sobre Prontuário Eletrônico – A Certificação de Sistemas de Registro Eletrônico de Saúde. São Paulo, 2012. Disponível em: <http://portal.cfm.org.br/Cartilha_SBIS_Pront_Eletr.pdf> Acesso em: 10 set. 2018.
COSTA, V.T; MEIRELLES, B.H.S; ERDMANN, A.L. Melhores práticas do enfermeiro gestor no gerenciamento de risco. Rev. Latino-Am. Enfermagem, Ribeirão Preto, v. 21, n. 5, set/out. 2013.
DEGRACE, Peter; HULET, Leslie. Wicked problems, righteous solutions. USA: [s. n.], 1990.
EDWARDS, C. Anatomia e fisiologia dos computadores. In: HANNAH, Kathryn J.; BALL, Marion J.; EDWARDS, Margaret J.A. Introdução à informática em enfermagem. 3. ed, Porto Alegre: Artmed, p. 26-41, 2009.
FRAGATA, José; SOUSA, Paulo; SANTOS, Rui Seabra. Organizações de saúde seguras e fiáveis/confiáveis. In: SOUSA, Paulo; MENDES, Walter (org.). Segurança do Paciente: criando organizações de saúde seguras. 1. ed. Rio de Janeiro: FIOCRUZ, 2014. v. 2, cap. 1, p. 17-36. Disponível em: <http://books.scielo.org/id/vtq2b/cpub/sousa-9788575415948.epub> Acesso em: 10 set. 2018.
FASSINI, P; HAHN, G.V. Riscos à Segurança do Paciente em Unidade de Internação Hospitalar: Concepções da Equipe de Enfermagem. Rev. Enferm UFSM, Rio Grande do Sul, v. 2, n. 2, p. 290-299, Mai/Ago 2012.
GIL, Antônio Carlos. Como elaborar projetos de pesquisa. 5 ed. São Paulo: Atlas, 2010.
GOMES, Adelia Quadros Farias. Iniciativas para segurança do paciente difundidas pela Internet por organizações internacionais: estudo exploratório, 2008. 135 f. Dissertação (Mestrado em Enfermagem) – Escola Nacional de Saúde Pública Sérgio Arouca ENSP. Rio de Janeiro, dezembro de 2008.
HOFFMEISTER, Louíse Viecili; MOURA, Gisela Maria Schebella Souto de. Uso de pulseiras de identificação em pacientes internados em um hospital universitário: aplicação na atenção hospitalar. Revista Latino-Americana de Enfermagem, Ribeirão Preto, v. 23, n. 1, jan/fev. 2015. Disponível em: <http://www.scielo.br/scielo.php?pid= &script=sci_arttext&tlng=pt> Acesso em: 10 set. 2018.
HOLLNAGEL, Elci. Proactive approaches to safety management. London: The Health Foundation; 2012.
International Civil Aviation Organization. Safety management. Annex 19 to the Convention on International Civil Aviation. Quebec: ICAO, 2013 Jul.
LAURENTI, Thaís Cristina et al. Gestão Informatizada de indicadores de úlcera por pressão. J. health inform, v.7, n.3, p. 94-8, set. 2015. Disponível em: <http://www.jhi-sbis.saude.ws/ojs-jhi/index.php/jhi-sbis/article/view/345> Acesso em: 31 ago. 2018.
LIMA, Helidéia de Oliveira; DUTRA, Elisabete Costa Reis. O gerenciamento de riscos na saúde: aplicação na atenção hospitalar. Revista de Administração Hospitalar e Inovação em Saúde, Minas Gerais, v. 4, n. 2, p. 87-90, 12 jul. 2010. Disponível em: <file:///C:/Users/Samsung/Downloads/1114-Texto%20do%20artigo-(1).pdf> Acesso em: 10 set. 2018.
KNAPP, Jack; ZERATSKY, John. SPRINT o método usado no Google para testar e aplicar novas ideias em apenas cinco dias. [S. l.]: Intrínseca, 2017. E-book.
KRAUSE, Thomas R., HIDLEY, J.H. Taking the lead in patient safety: how healthcare leaders influence behavior and create culture. New Jersey: John Wiley & Sons; 2009.
MAGALHÃES, Gildo. Introdução à metodologia da pesquisa: caminhos da ciência e tecnologia. São Paulo: Ática, 2005.
MAY, Chris Vander. Lições práticas sobre construções e lançamento de softwares aprendidas no dia a dia de trabalho no Google e Amazon. [S. l.]: Novatec, 2013. E-book.
MARQUES, Paulo Leonardo Ponte et al. Da pré-história à idade “mídia”: a evolução da tecnologia no desenvolvimento da humanidade. In: SANTOS, Zélia Maria de Sousa Araújo; FROTA, Mirna Albuquerque; MARTINS, Aline Barbosa Teixeira. Tecnologias em Saúde: da abordagem teórica a construção e aplicação no cenário do cuidado. 1. ed. Fortaleza: EdUECE, 2016. cap. 1, p. 24-42.
MORIMOTO, Carlos E. Hardware. O Guia Definitivo. [S. l.: s. n.], 2014. E-book.
MORIMOTO, Carlos. Manual de Hardware completo. [S. l.: s. n.], 2015. E-book.
NASCIMENTO, João Costa; DRAGANOV, Patrícia Bover. História da qualidade em segurança do paciente. História da enfermagem: revista eletrônica, Portugal, v. 6, n. 2, p. 299-309, 28 nov. 2015. Disponível em: <http://here.abennacional.org.br/here/seguranca_do_paciente.pdf> Acesso em: 10 ago. 2018.
NEVES, Lourdes Alexandrina Castro; MELGAÇO, Regina Maria Tavares. A identificação do paciente como indicador de qualidade, 2011. Dissertação (Mestrado em Gestão de Ambiente e Segurança em Estabelecimentos Assistenciais de Saúde) – Universidade Federal do Estado do Rio de Janeiro. 2011. Disponível em: <http://proqualis.net/dissertacao/o-paciente-como-indicador-de-qualidade> Acesso em: 30 ago. 2018.
PARANAGUÁ, T.T.de. B; BRAGA, Q.de. P; BEZERRA, A.L.Q et al. Eventos adversos: instrumento de gerencia de la asistencia para la seguridad del paciente en el servicio de urgências, Enferm. glob, v. 13, n. 34, p. 206-23, abr. 2014.
PEREIRA, Déborah Santana et al. A tecnologia como ferramenta promotora da saúde. In: SANTOS, Zélia Maria de Sousa Araújo; FROTA, Mirna Albuquerque; MARTINS, Aline Barbosa Teixeira. Tecnologias em Saúde: da abordagem teórica a construção e aplicação no cenário do cuidado. 1. ed. Fortaleza: EdUECE, 2016. cap. 3, p. 64-82.
PEREIRA, Maria das Dores; SOUZA, Diego Floriano de; FERRAZ, Fabiane. Segurança do paciente nas ações de enfermagem hospitalar: uma revisão integrativa da literatura. Revista Inova Saúde, Criciúma, v. 3, n. 2, p. 123-156, 3 nov. 2014. Disponível em: <http://periodicos.unesc.net/article> Acesso em: 10 ago. 2018.
PINOCHET, Luis Hernan Contreras. Tendências de tecnologia de informação na gestão da saúde. O Mundo da Saúde, São Paulo, v. 35, n. 4, p. 382-394, 29 jan. 2011. Disponível em: <http://bvsms.saude.gov.br/bvs//tendencia.pdf> Acesso em: 10 set. 2018.
PRESSMAN, Roger S.; MAXIM, Bruce R. Engenharia de software: uma abordagem profissional. 7.ed. Porto Alegre: AMGH, 2011. Disponível em: <https://pt.scribd.com/document/341109152/Engenharia-de-Software-Uma- Abordagem-Profissional-pdf> Acesso em: 10 set. 2018.
QUIERELLE, D. A. Criando Sites com HTML-CSS-PHP. Construindo um projeto- Iniciante. São Paulo, p. 6-10, 2012. Disponível em: https://www.clubedeautores.com.br/book/126851-Criando_sites_com_HTMLCSSPHP#.WTyJmJLyvcs Acesso em: 22 jan. 2019.
REDE BRASILEIRA DE ENFERMAGEM E SEGURANÇA DO PACIENTE. Estratégias para a segurança do paciente: manual para profissionais da saúde. São Paulo, 2013. Disponível em: <http://www.rebraensp.com.br/pdf/manualseguranca_paciente.pdf> Acesso em: 22 ago. 2018.
RUBIN, Kenneth. SCRUM Essencial um guia prático para o mais popular processo ágil. [S. l.]: Alta Books, 2018. E-book.
SABBAGH, Rafael. SCRUM Gestão ágil para projetos de sucesso. São Paulo: [s. n.], 2017.Disponívelem:file:///C:/Users/55119/Downloads/Scrum%20Gestão%20ágil%20para%20projetos%20de%20sucesso%20-%20Casa%20do%20Codigo.pdf. Acesso em: 20 nov. 2018.
SANTOS, Sérgio Ribeiro dos. Informática em enfermagem: desenvolvimento de software livre com aplicação assistencial e gerencial. Rev Esc Enferm USP, São Paulo, v. 44, n. 2, p. 295-301, 2010. Disponível em: < http://www.ee.usp.br/reeusp> Acesso em: 30 ago. 2018.
SANTOS, Dartagnan Sousa dos. Segurança do paciente: implantação de pulseiras de identificação na uti adulto, 2014. 31 f. Monografia (Especialização em Enfermagem) – Universidade Federal de Santa Catarina. Florianópolis, 2014.
SÃO PAULO. Lei n. 10.241 de 17 de março de 1999. Dispõe sobre os direitos dos usuários dos serviços e das ações de saúde no Estado e dá outras providências. São Paulo: Assembléia Legislativa do Estado de São Paulo; 1999. Disponível em: <http://www.al.sp.gov.br/repositório/legislação/lei/1999> Acesso em: 10 set. 2018.
SKLAR, David. Learning PHP 5. [S. l.]: Reilly, 2004.
SOARES, Bruno. Aprendendo a linguagem PHP. São Paulo: Ciência Moderna, 2013. E-book.
SOMMERVILLE, I. Engenharia de Software [recurso eletrônico]. 9. ed. São Paulo: Pearson Prentice Hall, 2011. Disponível em: http://www.ifcamboriu.edu.br/~catia/IA16/Engenharia_Software_3Edicao.pdf Acesso em: 24 jan. 2019
SOUSA, Paulino. Sistemas de Informação em Enfermagem: novos desafios, novas oportunidades. Rev. esc. enferm. USP, São Paulo. v. 46, n. 5, p. 1-2, out. 2012. Disponível em: <http://www.scielo.br/scielo.6001&lng=pt&nrm=iso> Acesso em: 31 ago. 2018.
SOUZA, Dalva Inês et al. Manual de orientações para projetos de pesquisa. Novo Hamburgo: Fundação Escola Técnica Liberato Salzano Vieira da Cunha, 2013.
SPERANDIO, Dircelene Jussara. Sistematização da Assistência de Enfermagem: Proposta de um software – protótipo, 2002. 75 f. Dissertação (Mestrado em Enfermagem) – Escola de Enfermagem de Ribeirão Preto da Universidade de São Paulo. Ribeirão Preto, 2002.
TORRES, Gabriel. Hardware e Redes. [S. l.: s. n.], 2010. E-book.
WATSON, D.S. Standardizing Wristband Colors. AORN J. v. 90, n. 3, p. 449-52, 2009.
WIKIPEDIA, Enciclopédia Livre. Microsoft Windows. Disponível em: Acessado em 05 de maio de 2019.
WORLD HEALTH ORGANIZATION. Collaborating Centre Patient Safety (Solutions). Washington, 2006. Disponível em: <http://www.who.int/patientsafety/Release.pdf> Acesso em: 07 ago. 2018.
WORLD HEALTH ORGANIZATION. Patient Safety Solutions Preamble, Genebra, Mai. 2007. Disponível em: <http://www.who.int/patientsafety/ patient safety /Preamble.pdf> Acesso em : 06 ago. 2018.
WORLD HEALTH ORGANIZATION. World Alliance for Patient Safety: forward programme. Genebra, 2005. Disponível em: <http://www.who.int/patientsafety/en/brochure_final.pdf> Acesso em: 06 ago. 2018.
WORLD HEALTH ORGANIZATION. World Alliance for Patient Safety, Taxonomy: The Conceptual Framework for the International Classification for Patient Safety: final technical report. Genebra, jan. 2009. Disponível em: <http://www.who.int/patientsafety/taxonomy/icps_full_report.pdf> Acesso em: 07 ago. 2018.
[1] Master’s degree of professional master’s program of the care process, Specialist in Patient Safety, Undergraduate nursing.
Submitted: July, 2019.
Approved: August, 2019.